Oh man, WordPress 5 is a thing now, and has been for a while now (since December 6th, for those keeping count at home), but have you updated to it? The tone of a lot of these security updates might make you think I’m joking, but I’m not. Last month, we had several clients on our server who had to contact us because their sites had been completely compromised, and in every instance, the dashboard looked something like this when we logged in to start the cleanup process.
![[Picard_Face_Palm.jpg] A WordPress dashboard with 15 pending updates, and a major version update notification](https://armortechs.com/wp-content/plugins/phastpress/phast.php/c2VydmljZT1pbWFnZXMmc3JjPWh0dHBzJTNBJTJGJTJGYXJtb3J0ZWNocy5jb20lMkZ1cGxvYWQlMkZpbWFnZSUyRmJsb2clMkZ3b3JkX3ByZXNzX3VwZGF0ZS5qcGcmY2FjaGVNYXJrZXI9MTY5Mzk4NjE2Ny0yODcyMSZ0b2tlbj02ZWY0ZDlhOGFhMWVhNDFi.q.jpg) Well, that may not be your problem, but it certainly doesn’t help.
Well, that may not be your problem, but it certainly doesn’t help.I’m certain I’ve said it before, and I’m certain I’ll say it again (and again, and again), but updates are important for security. The only good reason to skip an update is because you have done the research to determine that you don’t need the update, or that you are fully prepared for the risk involved in skipping it, and even then, you should probably be very sure of yourself and think on it again before you commit to skipping it.
Yes, it’s a little inconvenient, but it can be managed somewhat using automatic updates. That said, you will still need to manually initiate major version (like from 4 to 5), plugin, and theme updates. However, the tradeoff is that it is significantly less likely that you’ll have to talk to someone about recovering your site. And you should really want to avoid that, for a lot of reasons.
Reasons you should keep your CMS up to date:
- Most site compromising events are from “drive-by” hackers. These are folks who have a database of known vulnerabilities with certain frameworks, that scan whole servers at a time looking for someone they can run attacks against. Just by staying up-to-date, you can eliminate the possibility of this kind of attack almost completely.
- If you’re a business, your website is a form of marketing. If your marketing is pointing users to sketchy pharmaceutical sites, or if your website triggers the dreaded big red error in modern browsers, what does that say about your business?
- If your website contains sensitive data, like addresses, e-commerce transactions, and phone numbers (among others), you can be sued if that data is lost or accidentally disclosed due to a data breach.
- Site recovery services can be expensive. Armor is one of the lower-cost options available right now, and we charge $100 an hour for this service.
- Site recovery is not a guarantee of future protection. When we finish with a site, we promise that at the moment we hand it back over, it has no malware in it, is updated to the most current version, and has some form of software firewall to help protect it from future attacks, but if the user doesn’t keep the core or the software firewall up-to-date, they will very likely be spending another few hundred dollars to have us do the whole thing again in a few months.
- And this is a little more personal to our process, but I don’t pull punches on my event reports. I can’t, because if we’re not honest with you about how this happened, it’s much more likely you’ll end up in the same situation over and over again. That said, no one likes being called out, especially with incontrovertible evidence like time-stamped server logs, and if you’re doing your due diligence, I probably won’t have reason to.
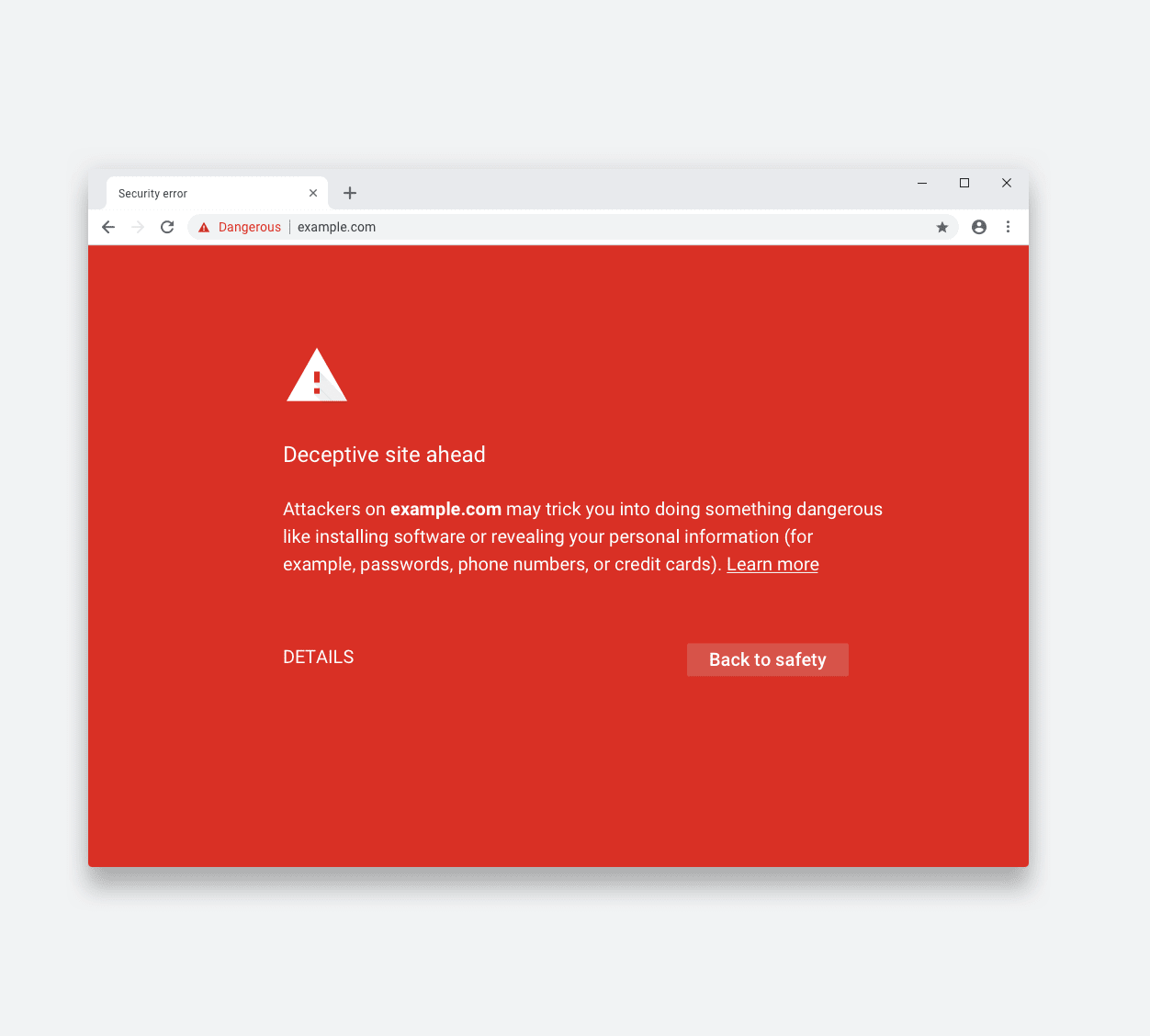 The Big Red Error
The Big Red ErrorAs a more specific note, more than a few of the clients who were compromised looked to have installed a vulnerable modification of the Gutenberg editor plugin that installed several backdoors into their WordPress installation. For those unfamiliar, Gutenberg is the name of the controversial new editor WordPress 5 uses by default. This plugin was not the official WordPress plugin, and we caution all users of WordPress to be wary of manually installing any Gutenberg plugin not authored by the “Gutenberg Team,” and be vigilant if you see a Gutenberg plugin appear that you did not install (and did not update to WordPress 5).
This particular collection of back doors was used both to serve malicious advertisements to visitors of the website and create phishing forms for various services like Amazon, Netflix, and eBay.
What Can We Do To Help?
As I mentioned above, we do offer site recovery services. We’ve been a hosting provider and web developers for years, so we’ve seen all sorts of website compromises, from remote code execution to poor user passwords. We have a collection of self-built and open-source tools that we use to complement our own hand cleaning of your website’s code.
In addition to that, if you’re a client hosted on our server, we maintain several backups of all websites on our server, which we can use to roll back your website to a point before the compromise happened. Security holes will still need to be closed, but this is often a very fast way to undo the damage done.
We provide and configure software firewalls designed to bolster your website’s security, be it our leaner and framework-independent Drawbridge solution, or for our WordPress users, the highly configurable and industry-leading WordFence plugin. We are also more than willing to take on the responsibilities of ensuring your website is and stays up-to-date.
If you’re interested in these or any of our other services, please fill out our contact form and get in touch with us today.

