Scam 1: Microsoft Pop Up Scam
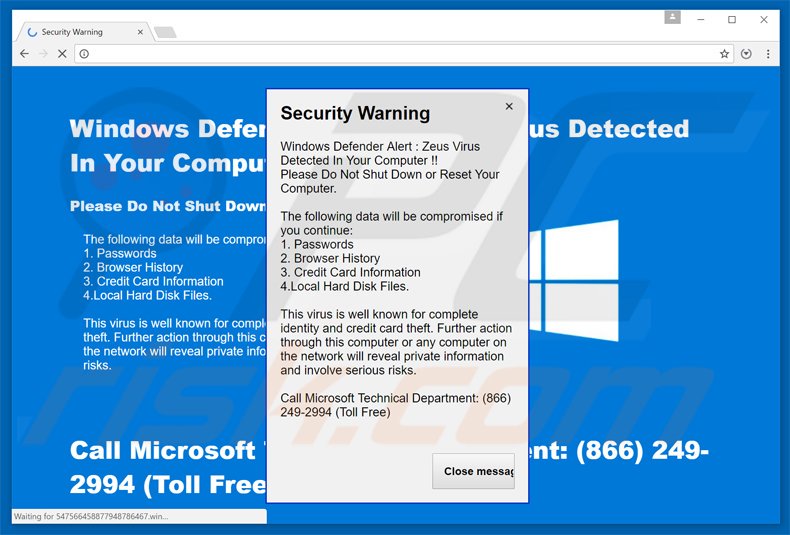
Commonly you’ll see popup windows that claim that your computer is broken or has been hacked and that you need to call a phone number in order to fix it. These scammers pose as Microsoft most often, and once you’re on the phone, they’ll sneakily find a way to make you give them remote access to your computer, and then as you for a strange form of payment (generally gift cards) in order to “fix” the problem. This is a common attack using your web browser and the code behind it in order to scare you. Whatever you do, DON’T let them into your computer—Microsoft will never contact you this way—they don’t know (or care) if your computer has been hacked, and they will not help you if it has been. If you’re a victim of this scam, immediately unplug your computer and take it to your local I.T. department to get it fixed.
Since this scam is performed in your web browser, you cannot trust anything on the screen, either. The “X” that would normally close the window may instead download a file without your permission. It is safest to close that window by using the keyboard shortcut ALT + F4, which force closes the window in question.
Scam 2: “I SAW WHAT YOU DID; now pay me Bitcoin”
Recently, we’ve seen a major uptick in the amount of email scamming that our server receives, and we’re sure you’ve gotten these emails too. They claim that they have your information, or they’ve seen what you’re doing on your webcam or in your web history. They tell you to pay them an amount of Bitcoin in order for them to delete the data, or they’ll send it to everyone in your contacts list.
Example:
“[NAME REDACTED], I know about the secret you are keeping from [NAME REDACTED] and everyone else. More importantly, I have evidence of what you have been hiding.
It’s just your bad luck that I stumbled across your misadventures while working a job around Los Angeles. I then put in more time than I probably should have looking into your life at [ADDRESS REDACTED]. Frankly, I am ready to forget all about you and let you get on with your life. And I am going to give you two options that will accomplish that very thing.
Option 1: Ignore the message and the aforementioned evidence will be sent to your wife, her friends, her family members and your neighbors.
Option 2: Pay a “confidentiality fee” of $8,600 in bitcoin and your secret remains your secret. I’m not looking to break your bank. I just want to be compensated for the time I put into investigating you.
The clock is ticking, [NAME REDACTED].”
The fact of the matter is that they almost always have no information on you, or the information they do have is publicly available online based on your email address. We recommend that you simply ignore this email and delete it. Unfortunately, most of these scammers are using email accounts that they don’t hold on to, so adding them to spam or a blacklist isn’t as helpful.
These emails are fraudulent. If you look closely, they don’t actually identify any of the information they have. Generally, it’s a bot or automation sending these out, waiting for even one person to reply to make their payout. Don’t reply to avoid getting more of them, and avoid being scammed.
Scam 3: Dating and Love Scams
These scams have evolved over the years but are a spinoff of the classic Nigerian Prince scams. You meet someone on a dating website or app, and you chat for a bit and get to know each other. They promise to meet you, but they say that they’re a bit short of the money and ask if you can give it to them. This should be a big RED FLAG to you. Sometimes these relationships also evolve very fast, with the person on the other end telling you they love you very quickly, sending you pictures that don’t seem right, and promising things they can’t possibly deliver. All of this should be a huge red flag.
We recommend that you take some time to really research this person and use the information they’re giving you to ensure they are who they say they are. Google everything, and if it seems too good to be true, it probably is. Here are some tools to help you with this:
- Google Reverse Image Search. Use this to take their picture to see where else that image comes up. You may find it in places with different names.
- Review the source of the email. There are headers in the email that can tell you the IP address and the time zone of the origin of the email. It may give you an idea of the real location.
- If you have a name or phone number, there are other sites to track people off of them to do a little background check.
- Find them on social media.
- Talk to your local, private I.T. department and give them the information for review. We have found several problems with fake images, fake passports, and fake people.
Scam 4: Phishing

Unfortunately, this form of “fishing” isn’t relaxing or entertaining. Phishing is when you receive contact that says there’s a problem with your account. You click a link, and you log into the website without making sure it’s actually the website you’re attempting to visit, and it turns out to be a near-exact copy of that website, hosted by someone else, that’s looking to steal your information.
By trying to log into your account on this fake website, you give the owner your email address and one of your passwords. They “phished” for your information, and you gave it to them, hook line and sinker. Now they can take that information and log into your real account and potentially any of your other accounts that use the same password. They can then change the password and effectively lock you out of your account.
When you click on links from your email or anywhere on the internet, check the URL twice and make sure that it’s the correct URL. When in doubt, type the URL in manually or create a bookmark, so you know that the website you’re visiting is the one you intend to visit. More often than not, these links look nearly identical but have something a little off—commonly, you’ll see something like: https://www.thebankwebsite.com.ru/account.
Did you catch that? It looks almost right, except for the .ru extension. This is just one example of a URL that looks almost correct, but it’s very important to make sure you’re at the right address when you’re navigating around the internet. Most of the websites you visit will probably be in your history too, so you can check there for an additional layer of security.
Scam 5: Bad Downloads
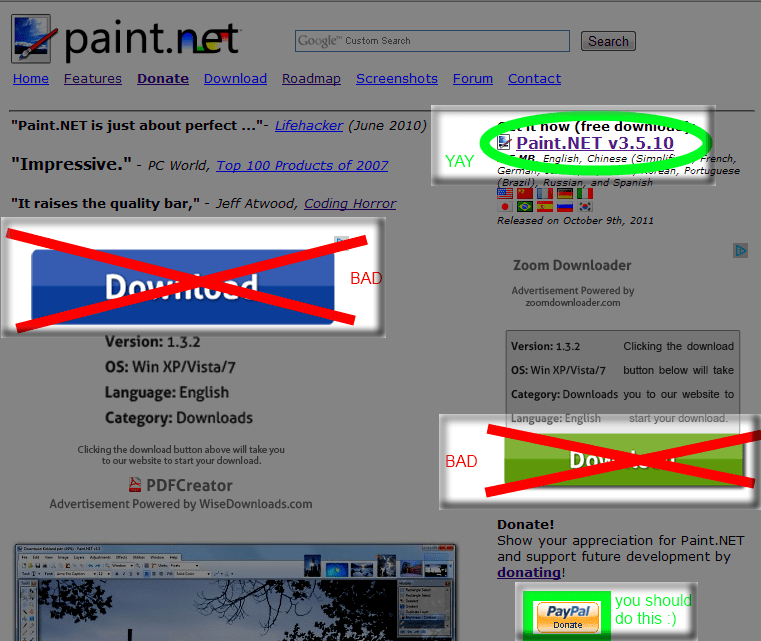
The internet is the largest network of information and solutions to problems we’ve ever had access to. You search the internet for basically everything, including software to make your life easier or more entertaining. Whatever you do, make sure the things you download are coming from a reliable resource and have file extensions that make sense.
For a little peace of mind before you download anything, ask for some references.
You search for everything on the internet. It may not be named correctly. You probably are going to download the first thing you find, and that might not be a good idea. Most of the viruses and malware are downloaded by mistake, thinking it was what they needed. You would not let just anyone babysit your child, right? What kind of reviews does the site have? Well, ask WOT. It is the Web Of Trust. If there is no info and no one knows much about the site that it is something you can download at your own risk. Just read and be careful.

