
INTRODUCTION
The problems with a password are obvious: the login system was first designed for time-sharing computers in the 1960s, working on mainframes that took up an entire lab. To use the computer, you tapped in your login name and password, which told the computer who was sitting at the terminal and which files to make available. Stealing someone’s password was good for a practical joke, but not much else: there was only one computer where you could use it, and not much personal information on display once you’d broken in.
But now, the right password can get you almost anything. You can read emails, order a new TV, or hijack cloud-storage accounts until you’ve accessed or deleted every trace of a person’s digital life. Two-factor authentication helps, splitting the password between two different systems and devices, but it’s far from perfect; in the end, it just means attackers have to crack two codes instead of one. No matter how you try to fix it, you run into the basic insecurity of the password at the root of it all.
One reason passwords are awful is that there are so many of them. Dashlane, a password manager company, found in a survey of its own customers that they have an average of 130 accounts with passwords. As a result, a lot of people use lazy passwords.
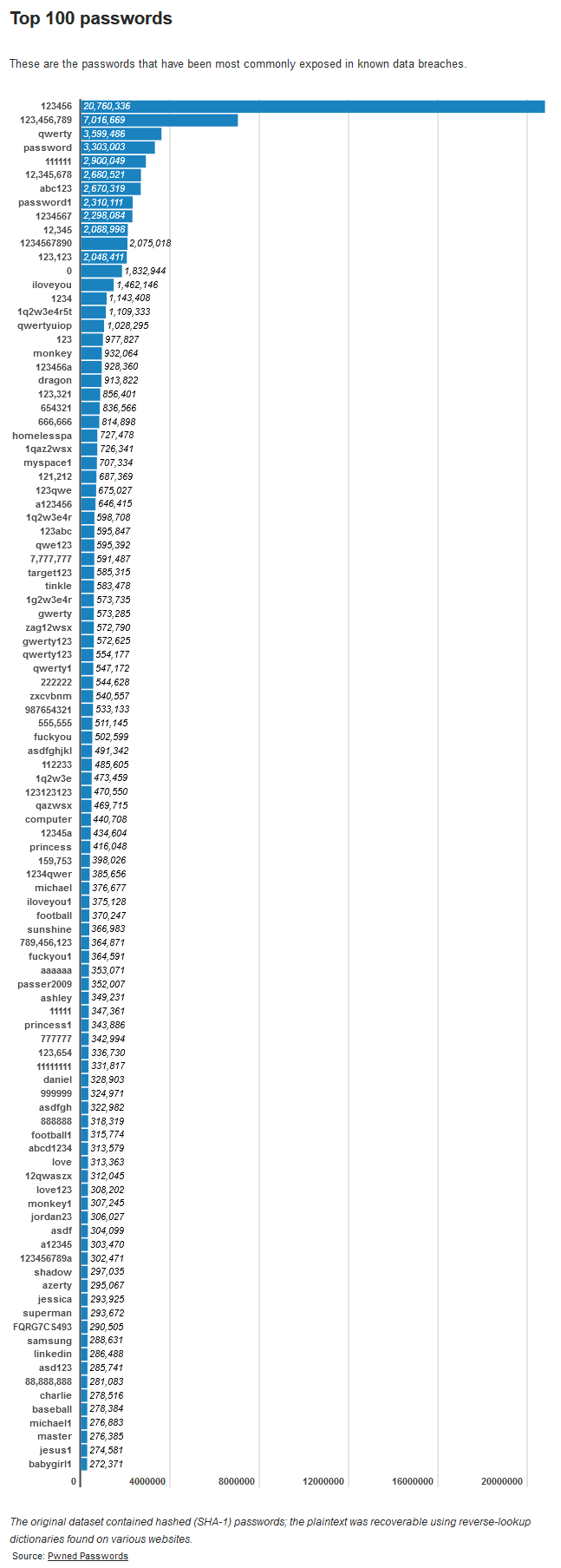
Another big issue? Finding the perfect password is difficult, as it requires a unique balance of “easy to remember” and “hard to hack.” And then you have to find that sweet spot over and over again. In the pursuit of safety, companies often require passwords to have a complex combination of capital letters, symbols, and other requirements. But those requirements can actually cause people to reuse their complex passwords or refuse to change them once they’ve committed them to memory. A password study by researchers at Virginia Tech found that slightly more than half of all users reused passwords or used slight modifications of passwords across a range of accounts. Password reuse, which is a major no-no according to security experts, is considered a major factor in easy-to-hack user authentication schemes.
Password Managers
Using a unique, strong password for every site is essential, and the simplest way to do this is to enlist the help of a password manager. A password manager installs as a browser plugin to handle password capture and replay. When you log in to a secure site, it offers to save your credentials. When you return to that site, it offers to automatically fill in those credentials. And, if you’ve saved multiple logins for the same site, the password manager offers you multiple account login options. Most also offer a browser toolbar menu of saved logins, so you can go straight to a saved site and log in automatically.
Getting all of your existing passwords into the password manager is a good first step. Next, you need to identify the weak and duplicate passwords and replace them with tough ones. Most password managers flag weak and duplicate passwords, and some offer help with the update process by automatically generating strong passwords for you. Plus, the best ones (Dashlane, Sticky Password, LastPass) sync across all of your Microsoft, Apple, iOS, and Android devices. For more information, check out Ryan’s post about passwords.
Killing Passwords
Recently, Microsoft said their Windows 10 S mode will strip out passwords by default. If you go through setup as recommended, you’ll never get a password option.
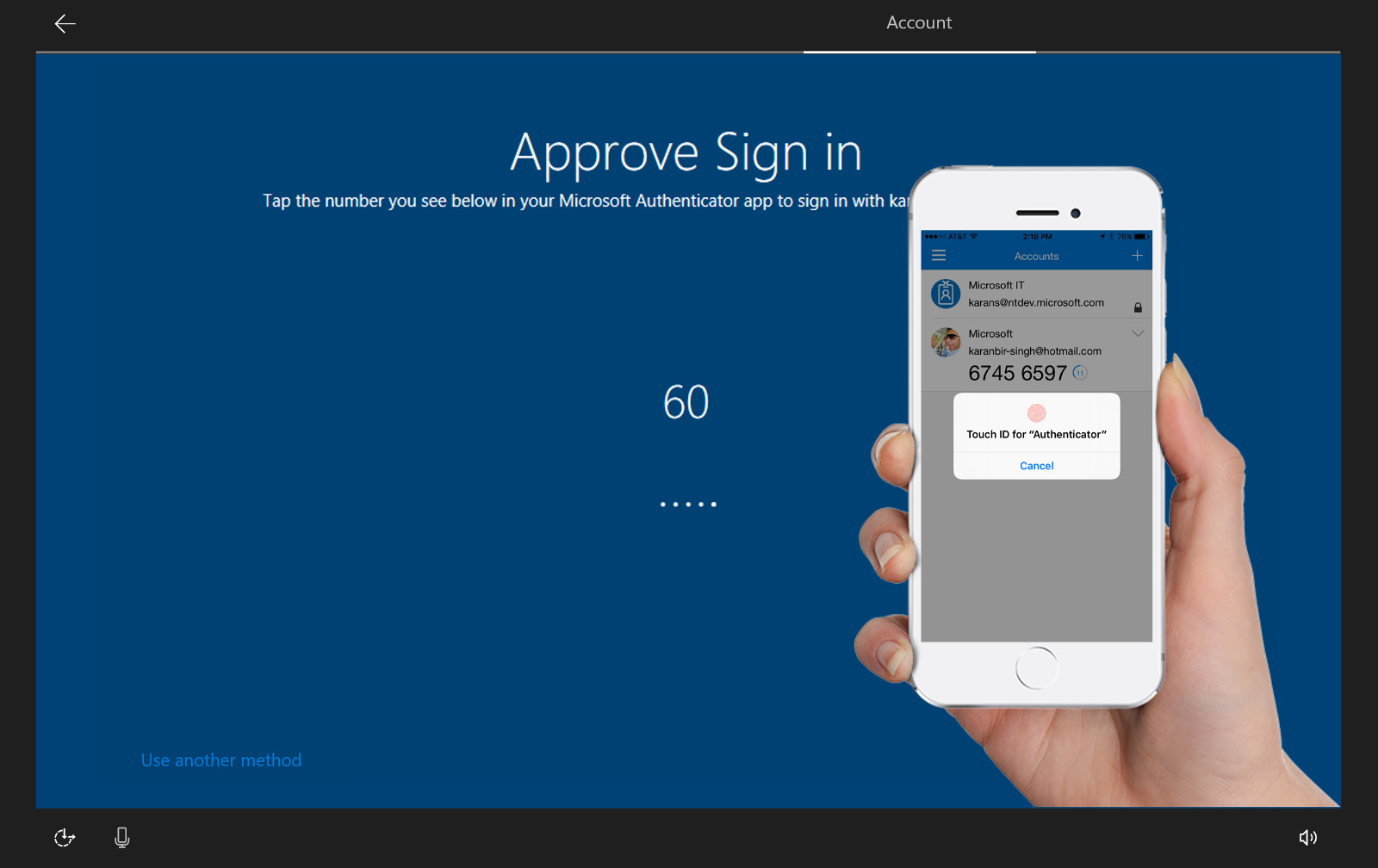
Microsoft is using its Authenticator App for Android and iOS, which spits out an 8-digit code every minute that’s uniquely keyed to your phone. It might not replace a good, strong, unique password, but an attacker would need to have access to a secured phone as well as your PC.
WebAuthn
The FIDO Alliance and W3C have launched a Web Authentication standard (WebAuthn for short) that makes it easier to offer truly unique encryption credentials for each site. That, in turn, lets you access virtually any online service in a PC browser through password-free FIDO Authentication, not just specific services. You can continue to use familiar methods like fingerprint readers, cameras, and USB keys, and it can serve both in place of and in addition to passwords.
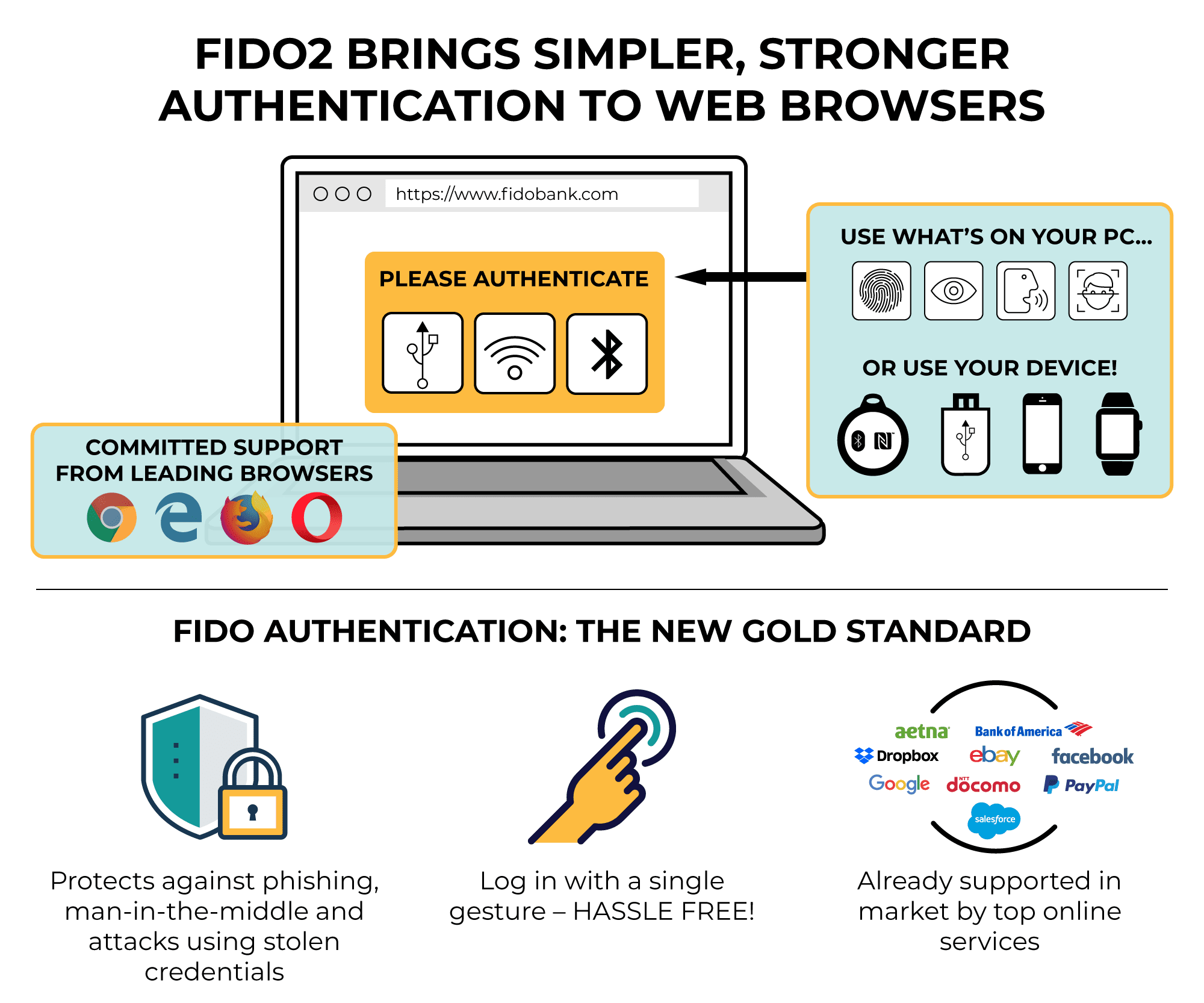
The functionality is being used right now in Mozilla Firefox and Google Chrome, and it should come to Microsoft Edge in the next few months. Opera has also publicly committed to the technology (there’s no mention of Apple bringing it to Safari). No, you can’t immediately forgo all your passwords, but this could let you depend on biometric logins much more consistently than you have in the past. The move could technically create a more secure Internet. As the rash of hacks, scams, and data breaches have shown over the last several years, passwords alone are not necessarily a suitable safeguard for data.
The idea behind WebAuthn is that you can use all manner of options in place of a password: a fingerprint, a webcam, a USB stick plugged into your computer, and so on. These login methods have been around for a number of years, but WebAuthn is designed to get them standardized across the web, and more seamlessly integrated into online logins.
It’s a logical extension of what browsers already do: remembering your passwords for you and auto-populating login fields whenever they pop up. Many of us already have all our login credentials securely stored in the browser, with something like a Windows or macOS account password stopping others from accessing the browser and opening up whatever sites they like.
With WebAuthn, this idea gets even simpler—with only a single tap required in a lot of cases. One added benefit is that the next time a batch of passwords spills out on the web, you don’t have to worry quite so much, because you’ve still got your fingerprint, the contours of your face, or a physical USB stick to fall back on.
 YubiKey
YubiKeyWhile we all wait for WebAuthn to be adopted universally, you can get something similar to it now. One option is the FIDO Universal 2nd Factor (U2F) standard, kind of a forerunner to WebAuthn—Gmail is one site that supports U2F, so instead of using an authentication app, you can use a verified USB stick instead. The tech also works with Facebook. This isn’t replacing your password though, but rather adding a two-factor safeguard.

