Is it really a Dark Web?
Well, first of all, not really. It’s been called many things, the dark web, the private web, the anonymous web, the Tor network, the onion network, they all are the same thing. And while some of the names like The Dark Web have connotations of nefarious doings and black markets best left to summer blockbuster movies, the concept itself was created for the benefit of the users.
As a whole, our society wasn’t exactly ready for what a global network like the internet could be when it first started to gain popularity. It’s created economic and technologic booms and busts several times as governments and corporations try to adapt to ideas like, customers can come from anywhere in the world, and even public information can be lucrative if you can interpret it in new but useful ways. As we find ourselves firmly in the age of big data here in the US, many users are starting to take issue with exactly how much data can be accurately guessed about our private lives based only on what we freely give websites access to about ourselves. But in reality, we’re far from the first people to face this issue, and in many other places, it’s the government, not corporations, with access to all this data, via scraping traffic from ISPs and locking down networks to prevent access to certain sites and services, and it was in reaction to these that a private network was developed.

What is it?
The dark web is a lot like the normal internet in a lot of ways. It uses the HTTP protocol for communications between clients and servers, and it allows those users to GET, POST, and UPLOAD items like you might find in normal server interactions, and for these reasons most existing server technologies are compatible with the TOR network. Facebook’s hidden service even has an SSL certificate applied to it (something of questionable use, but more on that later). How TOR differs from the normal internet comes down to the addressing scheme and the internetwork communication.
The internet is built on the back of an addressing scheme called DNS. It stands for Domain Name System and is a number of interconnected servers with domain names and IP address translations for those names. Think of it like a giant phone tree for getting anyone’s address. The first person you call might not have it, but they’ll have a good guess about someone else down the line who does, and they’ll keep calling until the information gets back to you. Once you have the address though, you simply go straight to that house.
TOR is a little different. The name a service on TOR has is actually a hash of the address that is used both to find the service and verify the other participant cryptographically once communication between the two has started, there’s still a process of looking up where an address is and then going there, but the journey is a little more interesting. Instead of just communicating directly with our destination, our TOR compatible browser will choose a random path between TOR nodes to get to where we’re going, these work a lot like proxies do on the normal internet, in that they are a way to anonymize your location and activities, but the difference is that these nodes are part of the overall infrastructure of the network, rather than things that are built on top of the network. And every connection to the service will utilize a different path through the nodes, further anonymizing the activity. This structure allows for many important uses like being able to access dissenting opinion blogs in China or accessing things your government has decided to block wholesale, like Facebook in Iran.
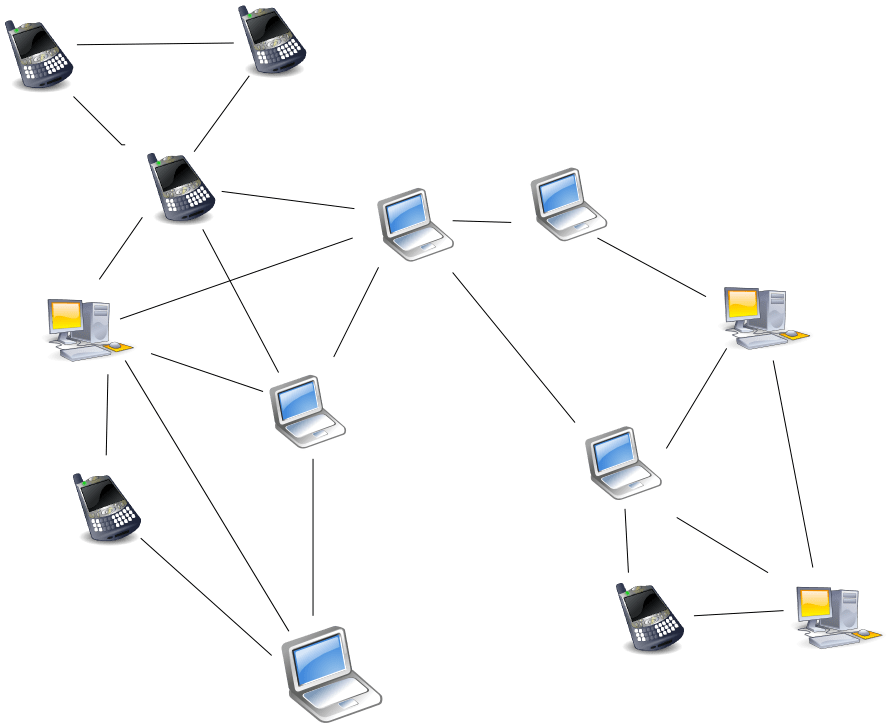 A Tor Network is, to an extent, not unlike a Peer-to-peer network, and if you are familiar with that networking model, this is not a bad visualization of how a Tor network works.
A Tor Network is, to an extent, not unlike a Peer-to-peer network, and if you are familiar with that networking model, this is not a bad visualization of how a Tor network works.And let’s talk a little more about Facebook in particular. Yes, Facebook’s business model in recent years has come under fire recently because it boils down to “we won’t directly sell your information, but we’ll profit directly off of giving it to other people,” but that does not undercut its value as a public forum for discussion, and as anyone can tell you, politics comes up a lot in those discussions, and in some countries, when the citizens are pushed too hard, those discussions can venture into territories that a government might not want to allow. In these cases, a system like TOR allows these citizens to continue having those discussions without fear of government reprisal.
Continuing the discussion from earlier about Facebook’s TOR SSL certificate, there is a lot of blowback from TOR users, since the fact that the TOR network is encrypted and authenticated by default seems to make the whole thing kind of useless, only serving to fool new users to the TOR network into thinking that one should be required for any TOR service they attempt to use, but that isn’t the end of it. One could argue that because Facebook’s TOR connection then bridges to a service that is accessible from the Internet, it’s simply an added measure to help protect those users’ privacy.
Now, that’s not to say that the technology is perfect, and everyone should be aware that a number of players have both contributed to and broken the technology, including governments and corporations the world over, but it’s a little like having a deadbolt on your house. It’s not unbeatable, but it’s certainly harder to break in with one, rather than if you just left the door unlocked. And for normal users, not committing criminal acts or affronts to human rights on our day-to-day internet use, it’s a good way of staying in control of own data, and it should be added to the tools available to the internet users in 2018, with proxies, VPNs, and the importance of SSL certificates.
It can also be a good place to look to for encrypted services like some chat projects that are using TOR to help protected user data. Just keep in mind that the TOR network is there for privacy, and while there is criminal activity present, most users will easily stay well clear of it.
Want to share your opinion on TOR, or Encryption?

